Vulnerability Assessments vs. Penetration Testing
The main difference between vulnerability assessments and penetration testing is in their approach and depth of analysis.
- Vulnerability assessments identify potential weaknesses in an organization’s IT infrastructure through high-level security scans.
- Penetration testing goes further by simulating real-world attacks to test the effectiveness of security measures and uncover how vulnerabilities can actually be exploited.
Unfortunately, many organizations struggle to keep pace with growing security threats due to limited resources. This often results in unpatched vulnerabilities, leaving systems exposed to cyberattacks.
A study by IBM revealed that the average time to detect a breach is more than 200 days—a stark reminder of the importance of effective vulnerability and penetration testing programs.
In this article, we’ll explore the differences between vulnerability assessments and penetration testing, and explain how the two approaches work best when combined.
What Is a Vulnerability Assessment?
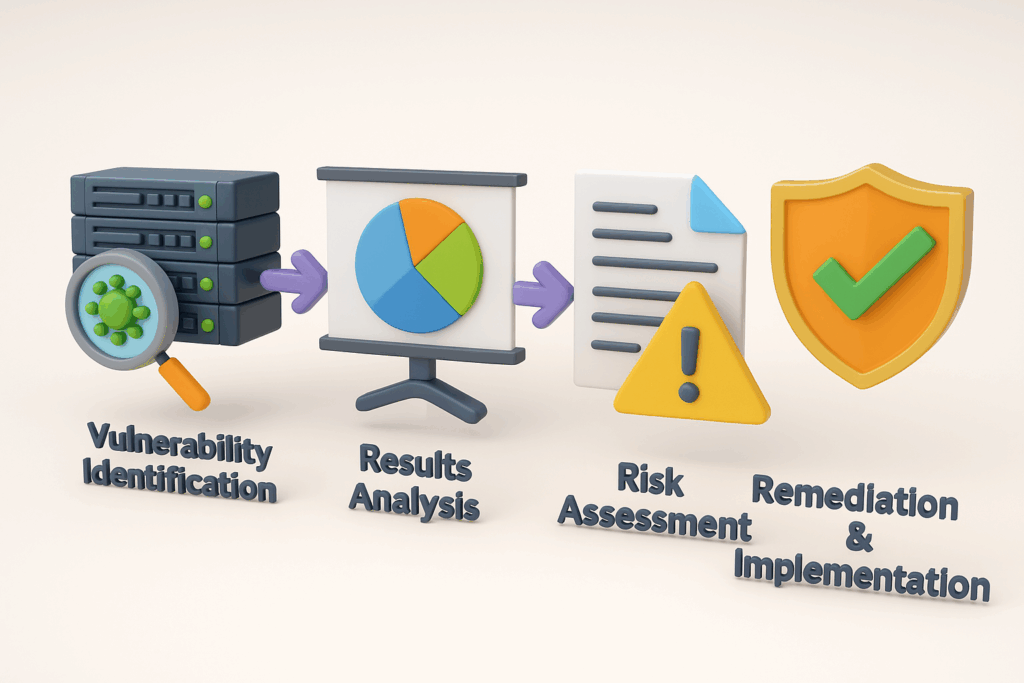
A vulnerability assessment is a security process that scans an organization’s IT environment to identify weaknesses that could be exploited by attackers.
For accurate and comprehensive results, organizations often perform credentialed scans against each host. The results provide a high-level overview of the security posture and highlight areas requiring remediation.
A complete vulnerability management program typically includes:
- Ongoing assessments to stay ahead of new threats
- Remediation of identified vulnerabilities
- Continuous monitoring to ensure improvements are effective
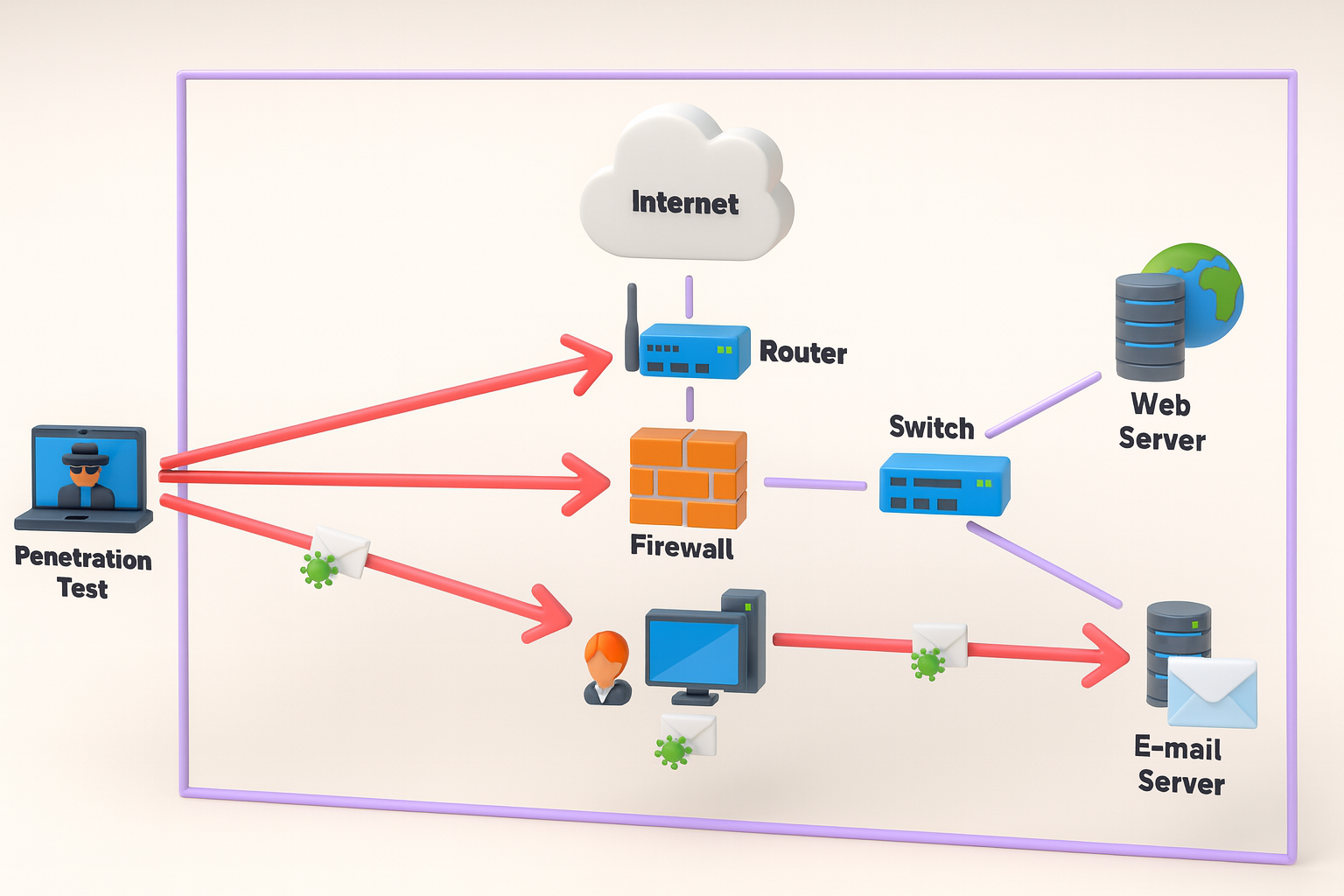
What Is a Penetration Test?
A penetration test (pen test) is a controlled simulation of a cyberattack conducted by security experts. Unlike vulnerability assessments, penetration tests:
- Actively attempt to exploit vulnerabilities
- Provide an in-depth analysis of how security gaps can be abused
- Help organizations measure the effectiveness of their defenses
Because of its offensive nature, a penetration test should always be approved by management before execution to ensure compliance and minimize risks.
Combining Vulnerability Assessments and Penetration Testing
Relying on just one method isn’t enough in today’s threat landscape. By combining vulnerability assessments with penetration testing, organizations gain:
- A comprehensive view of overall security posture
- A faster mean time to remediation (MTTR)
- Reduced risk across IT infrastructure
- A streamlined patch management process
Quarterly vulnerability assessments and annual penetration tests are no longer sufficient. Modern threats demand a more continuous and integrated approach.
Vulnerability Assessment Policy
A vulnerability assessment policy defines the organization’s guidelines for regular vulnerability scanning. It should outline:
- Scope of the assessment (systems, applications, and networks)
- Frequency of assessments
- Reporting and remediation procedures
Penetration Testing Policy
A penetration testing policy provides clear guidance for conducting ethical hacking exercises. It should include:
- Scope of the test (assets and environments)
- Testing frequency
- Reporting and remediation methods
How the Reporting Differs
Vulnerability Assessment Report: Offers a risk-based prioritization of identified vulnerabilities. It organizes scan results and recommends remediation steps.
Penetration Testing Report: Goes further, providing a narrative of attack scenarios, demonstrating how vulnerabilities could be exploited, and showing the real-world impact of weaknesses.
Why Mechsoft Technologies for Vulnerability Assessments and Penetration Testing?
Both vulnerability assessments and penetration testing are critical to a robust security program. While assessments help you find potential weaknesses, penetration tests show you exactly how attackers could exploit them.
By combining these two approaches, businesses gain a complete picture of their security risks and can act proactively to fix vulnerabilities before they are exploited.
Managing vulnerability scans and penetration testing in-house can be time-consuming and complex. That’s where a managed vulnerability management platform can make a difference.
At Mechsoft Technologies, our platform streamlines the process and improves efficiency. With real-time insights and expert recommendations, we help organizations stay ahead of evolving cyber threats, freeing up your internal teams to focus on mission-critical tasks.
